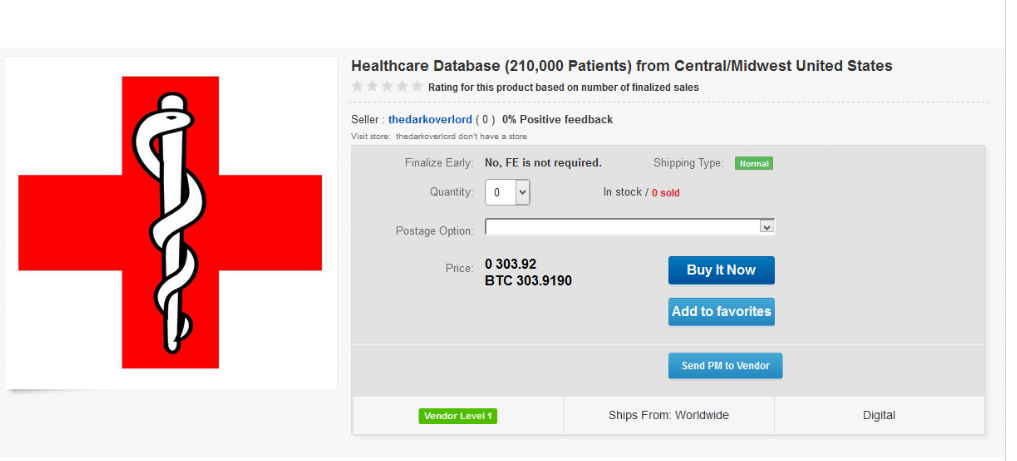
A screenshot from a “dark web” page provided by Breadcrumb Cybersecurity shows what potential buyers of medical records might see on an illegal e-commerce site. Contributed by Brian Horton
Written by
For many patients, the idea of having to go to the hospital can be scary enough. But one risk they may not be aware — aside from complications from a procedure or a bad diagnosis — is the theft of their identities or hacking of the very equipment their lives depend on.
Cyber attacks, however, are an all-too-real threat for hospitals and medical centers, the operations of which are far more sophisticated than one might suspect. Brian Horton is CEO of Fresno’s Breadcrumb Cybersecurity, which helps clients discover weak spots in their security and create strategies to better protect them. He said rather than facing stand-alone hackers, potential victims must often fend against groups supported by foreign governments.
“These are what we call ‘threat groups,’” Horton said. “Threat groups are well-organized entities outside of the U.S. Threat groups are usually, but not always, ‘mission state-sponsored,’ meaning they are helped and organized by the country they reside in, like Russia.”
Russia is one of the primary areas where threat groups originate, along with North Korea and Central Africa. In targeting health care, a threat group will often send a spam email in the guise of a legitimate message and once in, can access a patent’s medical records.
“What makes medical so popular is the non-perishable nature of that information,” Horton said. “So if you steal somebody’s credit card, well, you only have ‘x’ amount of days or hours to use that card. But if you steal somebody’s medical record, that lasts a lifetime.”
These hacks can be carried out over extended periods of time without hospital staff ever being aware of a breach. Once inside of a computer system, a hacker can also take control of equipment linked to the network and shut it down.
These medical device hijacks (or MEDJACKs) can wreak havoc on a hospital. They can also put patients’ lives in danger, essentially holding them hostage. Under these circumstances, a hospital has no choice but to pay the ransom, which is often in bitcoin.
Last year, the MEDJACK virus “WannaCry” made national news by hitting medical devices by Bayer AG.
Daniel Duffy, CEO and CIO of Valley Network Solutions in Fresno, said these breaches are almost always financially motivated — and with that in mind — hospitals and others can better prepare themselves.
“My overriding philosophy is follow the money. Nobody that I am aware of these days does these types of things for simply nefarious activities — there’s always some monetary incentive,” Duffy said. “So, if you can think of ways that somebody could harm you, or basically take your systems for ransom to their financial advantage, that will often help guide the decision making in what defenses you need to have in place and what systems might be attacked and what the motivations might be.”
To avoid a breach, Duffy and Horton gave several indicators on what to look for in an email that might contain a virus. One sign with seemingly professional emails will be subtle mistakes in the writing.
“Believe it or not, most of these emails that even look very persuasive are being written by somebody with English as a second language,” Horton said. “So there are nuanced spelling errors that you can spot within the email or words that are kind of used out of context.”
This is especially the case for someone with a trained eye, and Duffy recommended following one’s gut instinct if something seems out of place.
“For example, if you regularly receive and review job applications and something just jumps out at you as being abnormal,” Duffy said. “Maybe somebody’s applying for a position that doesn’t exist, but it looks like they’re communicating to you, but the position just doesn’t really fit with what you have open — that could be a tell.”
A further test to the link can be done as well, Horton said. It starts with not relying on the words in the actual link as displayed on the screen.
“If you hover your mouse over that link, it will pop up and show you where it will actually link you to,” he said.
Finally, one of the most important parts of preventing a breach is to stay on top of updates to cybersecurity and always check for weak points.
“Think like a bad guy and try and ask yourself what they might be motivated by and that might help you better scrutinize your weaknesses and defenses. And always take a layered approach to security. Anti-virus and firewalls are no longer by themselves sufficient.”
It’s hard to gauge whether this has been a real-world threat for local health care facilities. Horton said he has helped at least two hospitals that have had network breaches. Representatives from three local hospital groups — Saint Agnes Medical Center, Community Medical Centers and Kaiser Permanente Fresno Medical Center — declined to comment for this story.